How to identify a top cybersecurity consultant for small businesses?
Learn how small businesses can identify reliable cybersecurity experts and protect their systems with guidance from Top Cyber Security Consultants.
Cyber Lancers
3/16/20263 min read
Introduction:
In today’s digital world, cybersecurity has become a critical priority for businesses of every size. At Cyber Lancers, small businesses, in particular, often become prime targets for cybercriminals because they may lack the sophisticated security infrastructure used by large corporations. From phishing attacks and ransomware to data breaches and network vulnerabilities, cyber threats are evolving rapidly. This is why many organizations seek support from Top Cyber Security Consultants in Karnataka to protect their digital assets and maintain operational continuity.
About Us:
CyberLancers is a cybersecurity consulting and training organization dedicated to helping businesses protect their digital infrastructure. The company offers services such as vulnerability assessments, penetration testing, risk analysis, and managed security operations to strengthen organizational security. Along with consulting, CyberLancers runs a Cyber Academy that trains aspiring professionals through hands-on labs, real-world simulations, and expert mentorship. The organization regularly conducts cybersecurity awareness programs, workshops, and technical sessions that help individuals and businesses stay informed about emerging cyber threats while building practical skills needed in the cybersecurity industry.
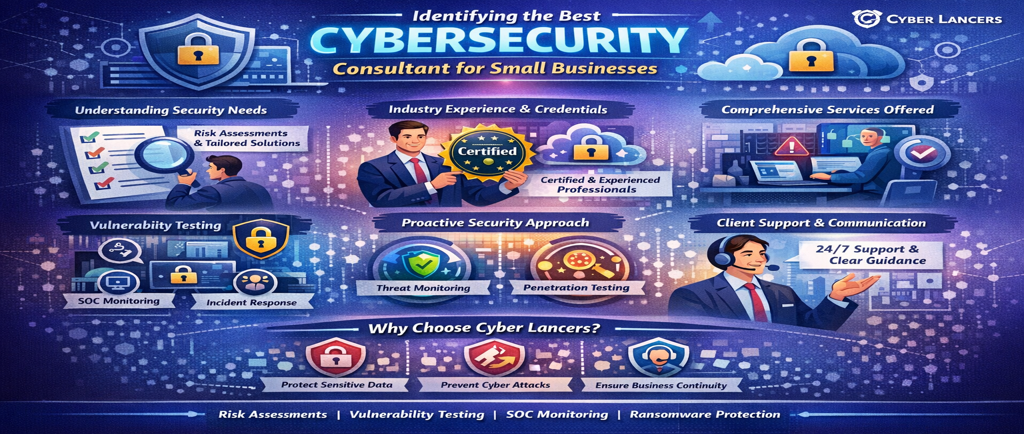
Understanding the Business’s Security Needs
The first step in identifying a reliable cybersecurity consultant is understanding your organization’s specific security requirements. Every business operates differently and faces unique threats depending on the nature of its operations, the type of data it handles, and its digital infrastructure.
A competent consultant begins with a comprehensive risk assessment. They evaluate your systems, networks, cloud environments, and internal processes to identify vulnerabilities. Consultants who offer tailored solutions rather than generic security packages often provide better long-term protection.
Evaluating Industry Experience and Expertise
Experience plays a vital role in cybersecurity consulting. Cyber threats constantly evolve, and experienced professionals have the practical knowledge required to handle emerging risks effectively.
When searching for small businesses, it should look for consultants who have experience working with organizations of similar size and industry. Consultants familiar with the challenges faced by startups, retail businesses, healthcare providers, or financial services companies can offer more relevant security strategies.
Certifications and professional credentials also indicate expertise. Industry-recognized certifications demonstrate that the consultant possesses the necessary technical skills and follows global security standards.
Reviewing the Range of Services Offered
A strong cybersecurity consultant should provide comprehensive security services rather than focusing on a single area. Cybersecurity is a multi-layered process that involves several aspects of protection and monitoring.
Common services offered by leading consultants include:
Security risk assessments
Network and infrastructure security audits
Security Operations Center (SOC) monitoring
Incident detection and response
Data protection and encryption strategies
Employee awareness and training programs
Businesses that partner with consultants offering integrated security services benefit from a more holistic approach to protection.
Assessing Their Approach to Proactive Security
One of the key differences between average consultants is their approach to proactive security. Cybersecurity should not only focus on responding to attacks but also on preventing them before they occur.
Effective consultants implement continuous monitoring, threat intelligence systems, and vulnerability management strategies. They regularly update security protocols and conduct penetration testing to identify weaknesses before hackers exploit them.
This proactive approach significantly reduces the chances of cyber incidents and helps businesses maintain stable digital operations.
Checking Client Support and Communication
Cybersecurity is not a one-time project. It requires continuous monitoring, updates, and improvements. Therefore, small businesses should evaluate the consultant’s communication and support capabilities.
Reliable consultants maintain transparent communication and keep their clients informed about potential risks, security updates, and system performance. They also provide clear guidance when responding to security incidents.
Quick response time and accessible support channels are important indicators of a dependable cybersecurity partner.
Conclusion:
For small businesses, protecting sensitive information and maintaining operational stability depends heavily on strong cybersecurity practices. Selecting the right consultant can significantly improve an organization’s defense against cyber threats.
Investing in the right cybersecurity partner today not only prevents potential financial losses but also builds trust with customers, strengthens digital resilience, and ensures sustainable business growth in the future.
FAQs:
What makes a cybersecurity consultant reliable for small businesses?
A reliable consultant performs risk assessments, proactive monitoring, and tailored security strategies.
Why should startups hire professional cybersecurity consultants?
Experts help prevent data breaches, protect customer information, and strengthen digital infrastructure.
How do Top Cyber Security Consultants in Karnataka support small businesses?
They provide threat monitoring, compliance support, and security architecture planning.
Do Cyber Lancers offer consulting services for small companies?
Yes, Cyber Lancers provides security audits, SOC monitoring, and vulnerability assessments.
What tools do cybersecurity consultants typically use?
They use SIEM tools, threat intelligence platforms, penetration testing tools, and network monitoring systems.
Can cybersecurity consultants help prevent ransomware attacks?
Yes, they implement firewall protection, endpoint security, and continuous threat monitoring.
Contact Info
info@cyberlancers.in
hr@cyberlancers.in
© 2026. All rights reserved Cyberlancers Pvt Ltd.
Phone:
Email:
Address:
MYRA School of Business, Near Infosys, opposite Power Grid, Yelawala, Karnataka 571130